XM Cyber is ready to welcome over 1,000 industry leaders, including the CEOs of 140 carefully vetted, private growth companies, at the Montgomery Summit 2020 presented by Maqcquarie. The event will be held on March 4-5 in Santa Monica, CA.
“We are the only ones to address the only crucial question for enterprises: ‘Are my critical assets really secure?’. We provide the only hyper-realistic breach and attack simulation (BAS) solution, an APT automated and continuous simulation and remediation platform – both on-prem and in the cloud,” said Richard Benigno, Senior Vice President Global Sales, XM Cyber.
Benigno will give a talk on Attack Simulation and Automated Purple Teaming in the Emerging Companies panel on March 4 at 1:30 pm.
Building on the fifteen-year legacy of the Montgomery Technology Conference, the Montgomery Summit is the top professional destination for entrepreneurs, growth company executives, global investment professionals, and corporate development executives.
To schedule a meeting, please email us at [email protected].
About XM Cyber
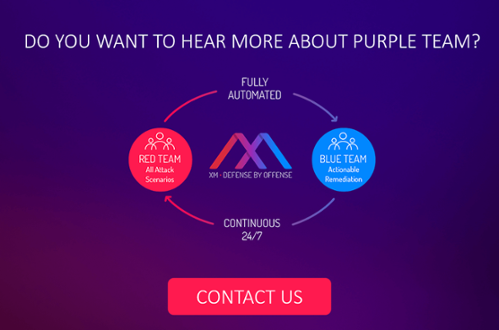
XM Cyber provides the first fully automated breach and attack simulation (BAS) platform to continuously expose attack vectors, from breach point to any organizational critical asset. This continuous loop of automated red teaming is completed by ongoing and prioritized actionable remediation. In effect, XM Cyber’s platform operates as an automated purple team, combining red and blue teams’ processes to ensure that organizations are always one step ahead of the attack. XM Cyber was founded by top executives from the Israeli cyber intelligence community and has offices in the US, UK, Israel and in Australia.
About XM Cyber for Attack Simulation
XM Cyber provides the first BAS platform to simulate, validate and remediate attackers’ paths to your critical assets 24×7. XM Cyber’s automated purple teaming aligns red and blue teams to provide the full realistic advanced persistent threat (APT) experience on one hand while delivering vital prioritized remediation on the other. Addressing real-user behavior and exploits, the full spectrum of scenarios is aligned to your organization’s own network to expose blind spots and is executed using the most up-to-date attack techniques safely, without affecting network availability and user experience.
Related Topics