The Identity Conundrum: Enforcing Least Privilege Access At Scale
Your CVE Count Is a Meaningless Metric
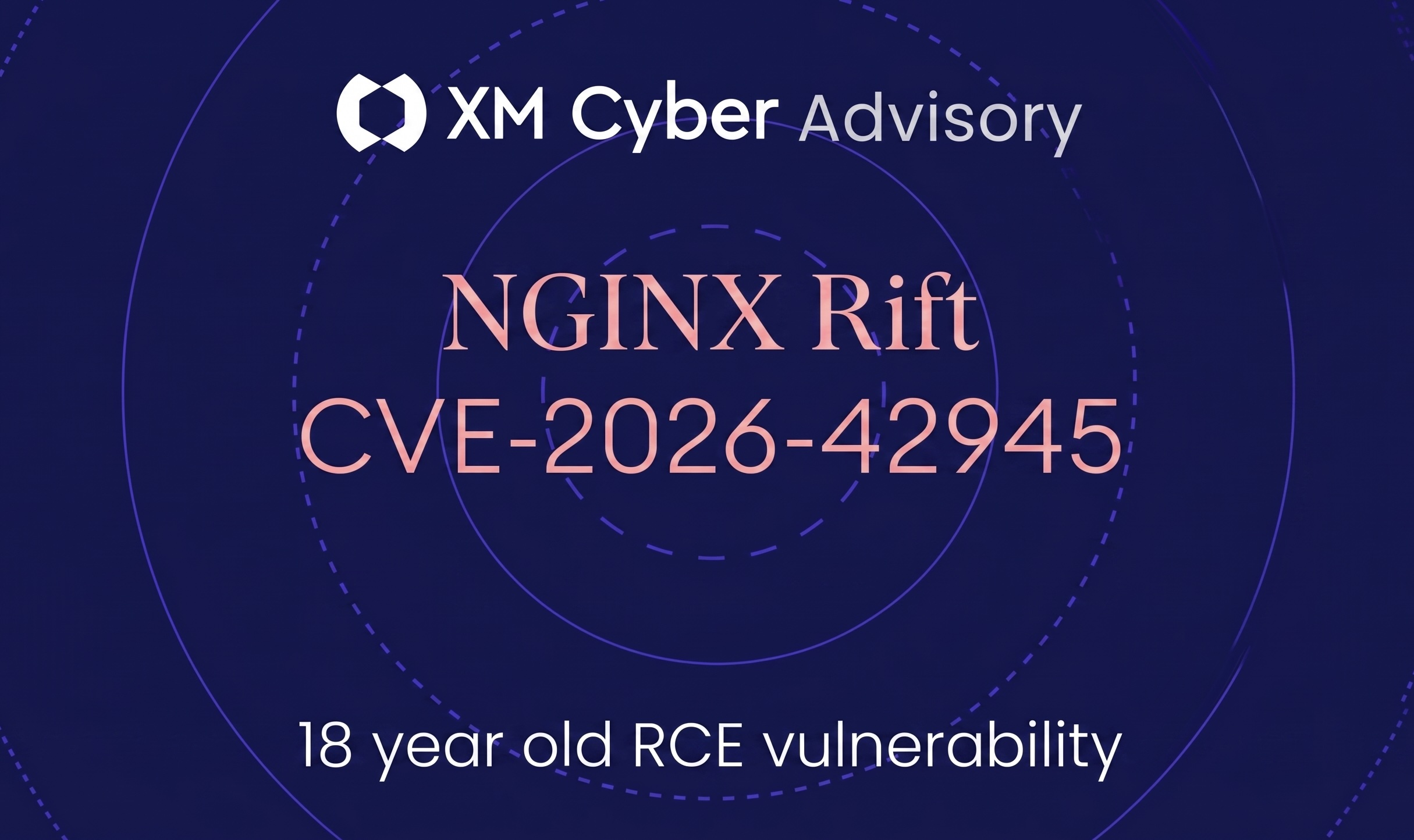
NGINX Rift Chain (CVE-2026-42945): Remote Code Execution (RCE) Discovered Leveraging 18-Year-Old Vulnerabilities
Contextualizing SOC Alerts with Exposure Intelligence
From Hunting Context to Hunting Threats: Using Exposure Intelligence to Accelerate SOC Investigations
Linux Kernel “Dirty Frag” Local Privilege Escalation (LPE), CVE-2026-43284 & CVE-2026-43500
Linux Kernel “Copy Fail” Local Privilege Escalation (LPE), CVE-2026-31431, Under Active Exploitation
Preparing for the Mythos Era – From Vulnerability Hunting to Exposure Management
XM Cyber Unveils PostureAI to Democratize AI-Powered SaaS Security for Google Workspace
Stop the SOC Burnout: Fixing the Alert Fatigue Crisis
See XM Cyber In Action