Prevent Attacks that Put your Business at Risk
Get ahead of attackers by continuously discovering, prioritizing, and fixing every validated exposure in YOUR environment before it’s exploited.
AI-powered attackers are cutting time-to-exploit from weeks to hours.
XM Cyber continuously surfaces every validated exposure that forms real attack paths, so defenders always move first.
The Only Integrated Exposure Management Platform to Show you Every Validated Attack Path

The product is easy to deploy, easy to handle and configure, and gives great and important insights from the attacker׳s point of view.
IT Security and Risk Management – Manufacturing

This tool allows you to define quick-win remediation but, more importantly, focuses on compromising paths to its most critical assets.
IT Security and Risk Management – Banking

Best CTEM feature solution currently on the market. The usability and product features are innovative to me and work well.
IT Security & Risk management – IT Services
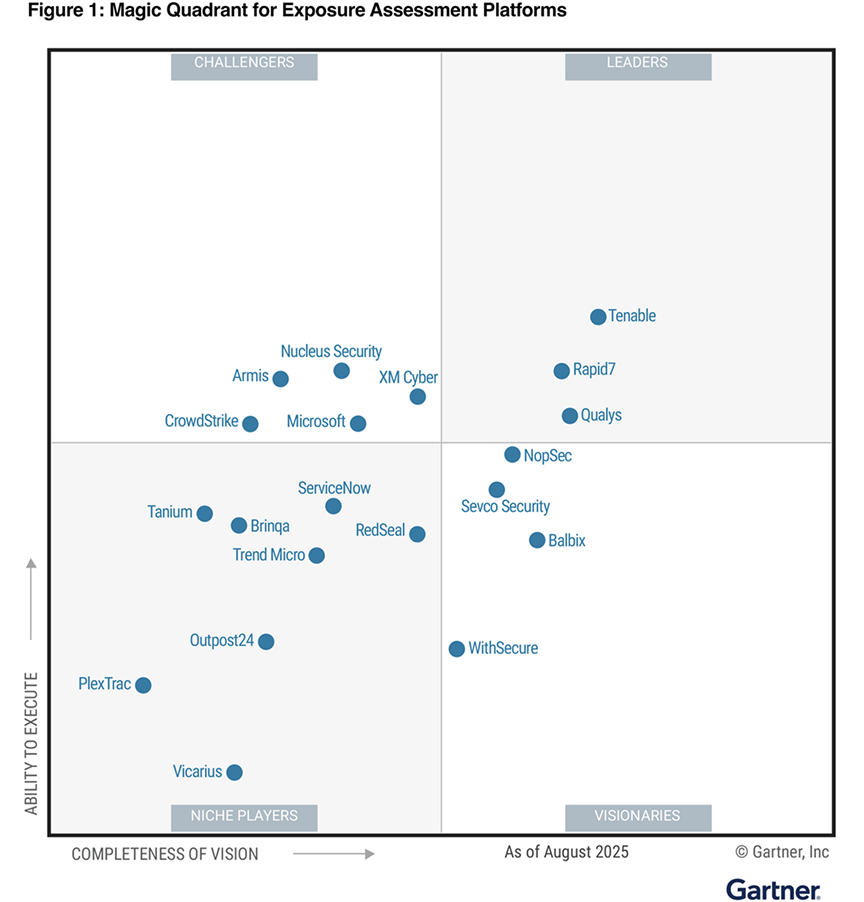
Challenging the Status Quo
XM Cyber Named a Challenger in the First-Ever 2025 Gartner® Magic Quadrant™ for Exposure Assessment Platforms
Meeting the World’s Leading Compliance Standards




Secure your Business Initiatives
Eliminate Risk Across the Full Attack Surface With Continuous Exposure Management
Cyber Risk Reporting
Communicate effective risk reduction and security posture improvements to leadership
Audit & Compliance
Achieve continuous compliance with top standards and regulations across your security ecosystem
Total Economic Impact Study™ of XM Cyber
394%
Return on investment, with payback in under 6 months
$12.4M
Reduction in remediation, fines, lost revenue, and brand reputation costs
$1.4M
Reduction in costs associated with penetration testing
90%
Reduction in the likelihood of experiencing severe breach
The Most Comprehensive Solution for Adopting CTEM
Adopt and maintain the Continuous Threat Exposure Management (CTEM) framework by delivering Exposure Assessment and Exposure Validation in a single platform.
Explore the five stages of CTEM:
Scoping
Identify your most critical assets and which business processes they map to in order to prioritize based on risk to the business.
Discover
Ensure holistic, continuous discovery:
- CVEs, misconfigurations, identity and access exposures
- Across on-prem and cloud environments
- From the external attack surface to the internal network
Prioritization
Focus on what to fix first in order to prevent high-impact attacks:
- Threat intelligence
- Likelihood of exploit in your environment
- Criticality and business impact
Validation
- Assess the exploit potential of exposures based on:
- Visualization and analysis of the attacker’s view
- Security controls’ configuration monitoring
Mobilization
Accelerate remediation and improve collaboration by providing:
- Context of business impact and urgency
- Remediation guidance, alternatives and validation
- Integration with ticketing, SIEM, and SOAR
Get a Demo Today!
Eliminate Risk Across the Full Attack Surface With Continuous Exposure Management