Discover cyber exposures that lead to successful ransomware attacks and prevent them in advance, with Exposure Management
Ransomware groups are looking for ways to reach your critical assets, to increase their chances of getting a higher ransom payout. For the same reason, they have begun employing the double extortion technique, where before encrypting your data, they exfiltrate it and then threaten to leak it online. Searching for routes to reach your critical assets, attackers are lying low, propagating the network as a result of misconfigurations, unpatched vulnerabilities and mismanaged credentials.
Existing security controls are often siloed and provide fragmented visibility of your critical assets and the attacker’s journey. Attackers take time to explore your cyber exposures but knowing which exposures put your critical assets at risk above others is challenging. Knowing what to fix first and which junctions in your network can be more damaging than others as many attack paths traverse through these is key to sabotaging any attack. Focusing on the attacker’s path results in better resilience as well as better ROI from your existing security tools.
Get the attackers’ perspective of your environment
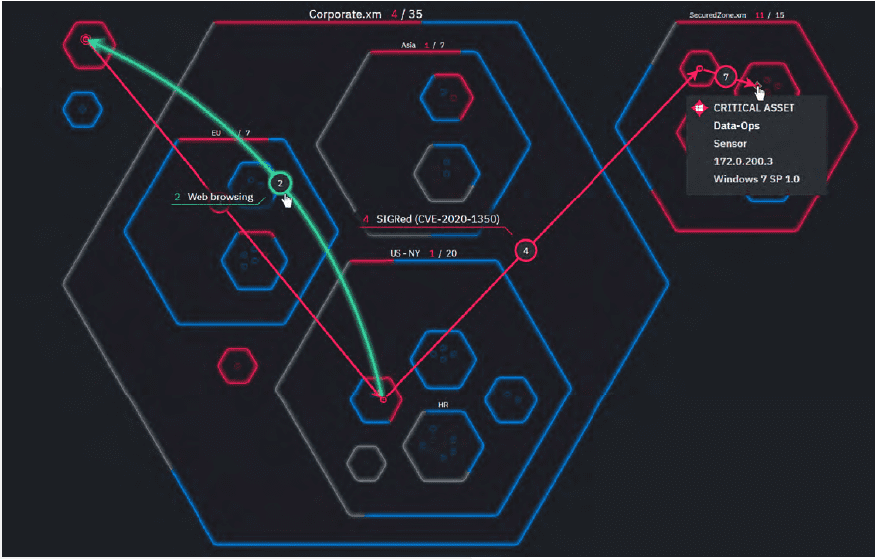
The XM Cyber Exposure Management Platform runs continuous and safe ransomware attack modeling, enabling you to see your environment through the eyes of the attackers and to gain complete visibility of the actual attack surface. By assuming breach, the platform highlights the cyber exposures that enable attackers to stealthily move within your network, on their path to take control of your critical assets, and to exfiltrate and encrypt data.
Early visibility of all possible ransomware attack paths and cyber exposures in your network will help you prioritize and focus resources on fixing the security issues that have the biggest impact on the success or failure of a ransomware attack.
- Illuminate and disrupt ransomware attack paths, in the cloud or on premises
- Close the gaps ransomware groups can use to compromise your network
- Continuously monitor and know what to fix first to prevent attacks
- Efficiently reduce the risk and impact of ransomware attacks

Highlight choke points
The key devices and entities that many attack paths traverse through and facilitate access to your critical assets and data
Ensure safe, fast and cost-effective remediation
XM Cyber Exposure Management solution automatically generates an actionable remediation plan that prioritizes the required actions for cost-effective, safe and speedy disruption of current and future ransomware threats. Follow the step-by-step guidance to ensure optimized use of resources for fixing exposures, as well as continuous enhancement of your security resilience and improved operation of your existing security tools. It could be as simple as removing a user from the directory.

Follow the step-by-step remediation plan to harden your environment and improve your security posture
The XM Cyber Exposure Management Platform proactively makes it harder for ransomware and malicious groups to access, exfiltrate and encrypt your data, by greatly reducing the attack surface, disrupting attacks in the making and enhancing your resilience.


